Extensible policy as code
Checkov is a command-line interface (CLI) that scans infrastructure as code (IaC) for misconfigurations and exposed secrets. Coverage includes Terraform®, Terraform plan, CloudFormation, Kubernetes®, Dockerfile, serverless and ARM templates and more.
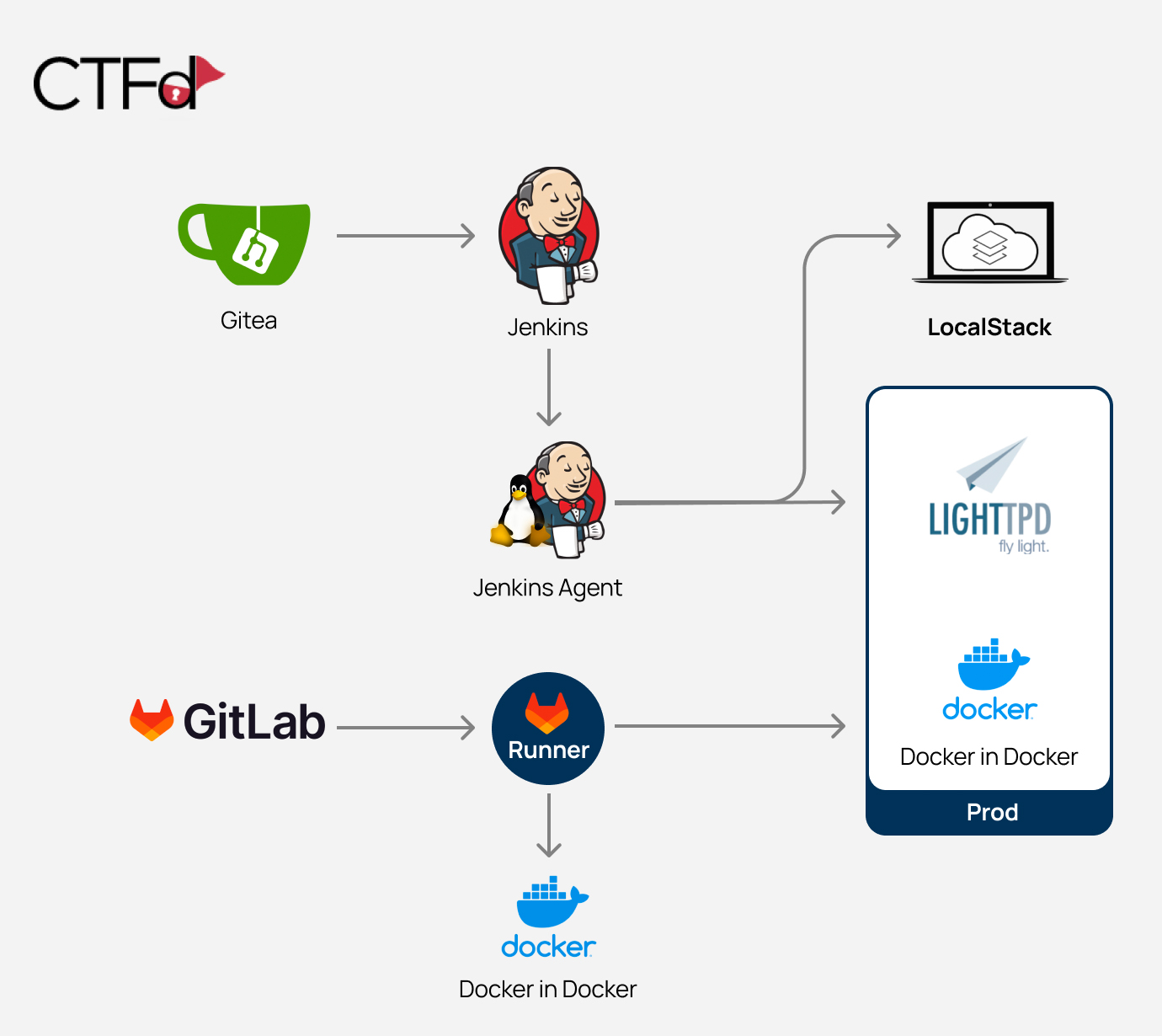
Integrate as a guardrail for CI/CD pipelines.
Include graph-based analysis for context-aware policies.
Add custom policies in Python or YAML.
Python 8570 1314